Paying for things online is now a speedier and more streamlined process than ever before, but that means less time for it to be made secure by the cybersecurity measures. With the digital economy expanding across borders, payment gateway fraud attacks are also escalating in both volume and complexity while becoming more and more automated. Where it used to be a few lone stolen cards, now bank accounts are hit across KYC accounts en-masse in coordinated bot attacks and exposed API-level vulnerabilities or synthetic IDs.
TransUnion’s H2 2025 Global Fraud Report found that companies worldwide lost an average of 7.7% of annual revenue to fraud in 2024.
Global ecommerce fraud losses are projected to grow substantially year over year. According to Juniper Research, ecommerce fraud expenses will exceed $107 billion by 2029
For those businesses that depend on card-not-present transactions, the writing is on the wall: ignoring payment gateway risk mitigation is no longer optional. It’s a fundamental element of payments infrastructure architecture, and long-term risk management.
In the European Economic Area, payment fraud hit €4.2 billion in 2024, even as strong authentication reduced some fraud types.
What Is Payment Gateway Fraud?
Transaction security risk describes the criminal process of taking control of the transaction chain between a customer, merchant, and payment processor. The gateway itself is rarely compromised; instead, fraudsters exploit the way that gateways validate, route and authorize transactions.
Unlike in-store scenarios, which are typically card-present and are based on something the customer has in their possession (the payment cards themselves), gateway-based fraud usually happens within a card-not-present context using proxy signals for identity, instead of a physical card.
And that’s why payment transaction risk mitigation focuses on behavior, transaction context, and intent rather than merely card validity.
Why Payment Gateway Fraud Is Growing
Over the past few years, fraud has grown faster than online commerce itself. Industry research consistently shows that fraud losses increase as checkout friction decreases and new payment methods are introduced.
Several structural factors are driving this growth:
- The rise of real-time payments and instant authorization
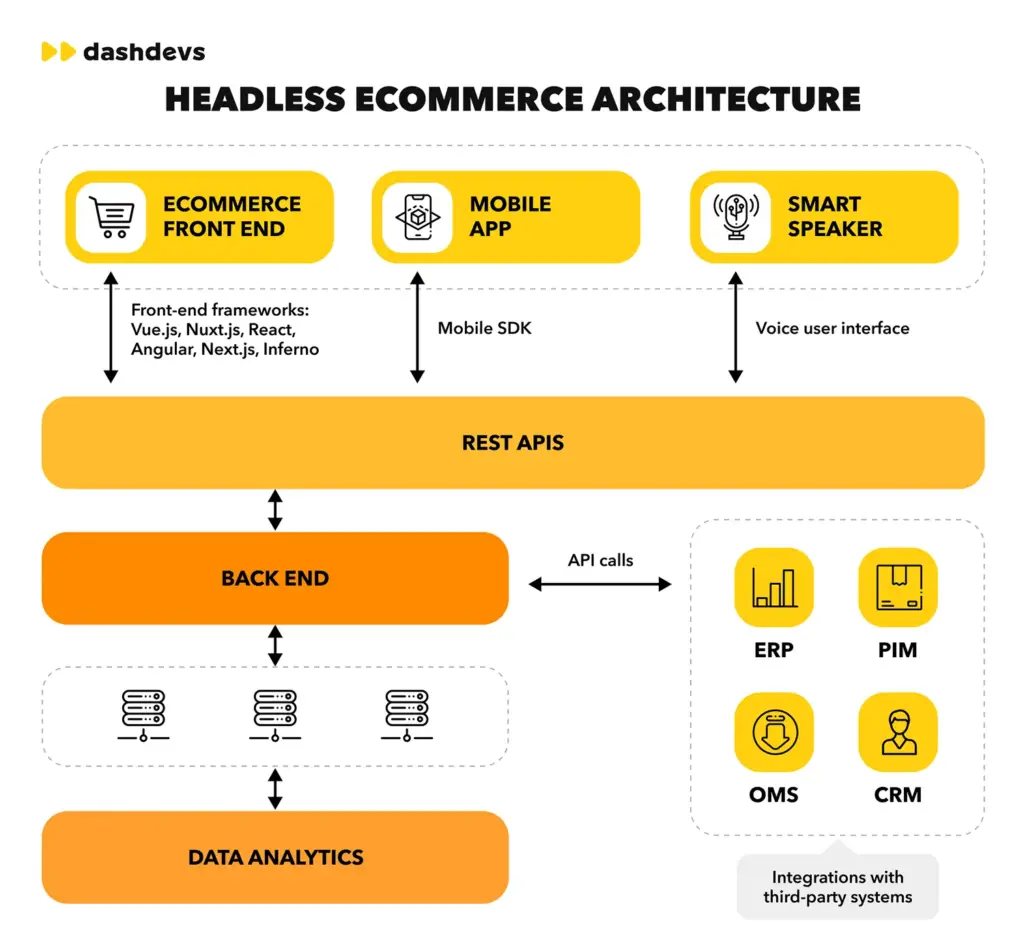
- Increased use of APIs and headless checkout architectures
- Bot-driven automation that allows fraudsters to test thousands of cards per minute
- Globalization of eCommerce, which complicates risk assessment across regions
By 2026+, fraud is no longer dominated by manual attacks. Instead, it is characterized by scale, speed, and data-driven abuse of payment systems.
Types of Payment Gateway Fraud
Modern payment processor fraud manifests in several recurring patterns. Understanding these attack types helps businesses map defenses more effectively.
Card Testing and BIN Attacks
Fraudsters use bots to submit rapid, low-value transactions to test stolen card numbers or identify valid BIN ranges. If successful, cards are later used for larger purchases or resold.
Account Takeover Fraud
Attackers gain access to legitimate customer accounts using stolen credentials. Once inside, they initiate transactions that appear trustworthy, making detection more difficult.
Synthetic Identity Theft
Fraudsters combine real and fake data to create identities that pass basic verification checks. These identities are used to open accounts and process transactions until credit limits are reached.
Bot-Driven Fraud
Automated scripts mimic human behavior, rotating IPs, devices, and session data to bypass basic security filters. Bot-driven fraud is especially dangerous for APIs and headless checkouts.
Friendly Fraud and Chargeback Abuse
Not all fraud comes from criminals. Some disputes result from customers denying legitimate transactions, increasing chargeback rates and financial risk for merchants.
Best Payment Gateway Fraud Prevention Tools 2026
In 2026, payment transaction risk mitigation requires more than static rules or post-transaction checks. As attacks become automated, API-driven, and cross-border, the most effective fraud prevention tools operate in real time and address multiple attack vectors simultaneously.
The best payment gateway transaction security tools fall into several core categories, each protecting against different types of abuse.
Core Fraud Prevention Tool Categories
| Tool Category | Protects Against | Most Effective For | Key Limitations |
|---|---|---|---|
| AI & Behavioral Fraud Detection | Card testing, synthetic identities, abnormal transaction patterns | Dynamic, evolving fraud attacks | Requires data volume and ongoing tuning |
| Bot Mitigation & Traffic Intelligence | Automated card testing, credential stuffing, API abuse | High-volume and headless checkouts | Must continuously adapt to new bot behavior |
| Transaction Velocity & Rate Limiting | Brute-force retries, rapid authorization attempts | Early-stage attack containment | Ineffective alone against low-and-slow attacks |
| Authentication & Step-Up Verification | Account takeover, unauthorized transactions | High-risk sessions and login flows | Can reduce conversion if overused |
| Chargeback Monitoring & Dispute Analytics | Friendly fraud, hidden fraud patterns | Post-transaction insight and optimization | Reactive rather than preventive |
How These Tools Work Together
This layered approach allows merchants to block fraud without introducing unnecessary friction for legitimate customers.
- Behavioral and AI-driven detection identifies suspicious patterns early
- Bot mitigation stops automated abuse before authorization costs escalate
- Velocity controls limit attack scale during probing phases
- Authentication tools reduce liability and unauthorized access
- Authentication tools reduce liability and unauthorized access Chargeback analytics close the feedback loop and refine controls
No single tool can fully ensure payment gateway transaction security. The most effective fraud prevention strategies in 2026 combine multiple layers:
What to Prioritize in 2026
When evaluating payment gateway transaction security tools, businesses should prioritize:
- Real-time decisioning at the authorization level
- Coverage for API and headless checkout environments
- Adaptive controls rather than static rule sets
- Visibility into raw fraud signals, not just risk scores
Fraud prevention is no longer a secondary security feature – it is a core component of payment gateway architecture and long-term revenue protection.
How Fraudsters Target Payment Gateways
Attackers rarely target gateways directly. Instead, they look for weak points around the gateway layer:
- Insecure API endpoints or excessive retry allowances
- Lack of velocity limits on transaction attempts
- Insufficient monitoring of failed authorization patterns
- Overreliance on static rules instead of behavioral analysis
Once weaknesses are identified, attacks are scaled rapidly. This is why real-time transaction monitoring is critical: delays of even minutes can result in thousands of fraudulent attempts.
Technical Entry Points Commonly Exploited in Gateway Attacks
Although fraud events are depicted in business terms, the majority of them succeed on the basis of very specific technical gateway layer vulnerabilities.
A very common vector used is “excessive retry tolerance”. Without adaptive authorization, if gateways allow repeat approval attempts, attackers can test card numbers and/or credentials at scale without raising alarms. This is particularly prevalent in API-driven or headless commerce ecosystems.
Also, the lack of a clear boundary between external-facing checkout logic and backend transaction processing provides another weak spot. Loose API keys, overly open endpoints, or a lack of request validation create opportunities for abuse rather than direct penetration of the gateway.
Inconsistent error handling is another area where scammers can take advantage. Different response codes for different failure causes can accidentally reveal data about card validity, balance and/or authentication. At the scale of operation, these signals suffice for automatic optimization of attacks.
In terms of security you need more than the anti-fraud rules/ You need disciplined API design, robust rate limits, and consistent response normalization across all transaction paths.
Although fraud events are depicted in business terms, the majority of them succeed on the basis of very specific technical gateway layer vulnerabilities.
Fraud Types vs Prevention Layers
Different payment gateway transaction security risks require different prevention layers. No single control can stop every attack. Effective fraud prevention depends on aligning specific fraud vectors with the defensive mechanisms best suited to detect or block them.
The table below illustrates how common payment gateway transaction security risks map to core prevention layers across the transaction lifecycle.
Fraud Types vs Prevention Layers Matrix
| Fraud Type | AI & Behavioral Analysis | Bot Mitigation | Velocity & Rate Limits | Authentication (3DS / MFA) | Chargeback Monitoring |
|---|---|---|---|---|---|
| Card Testing and BIN Attacks | High effectiveness | High effectiveness | High effectiveness | Low effectiveness | Not effective |
| Account Takeover (ATO) | High effectiveness | Limited effectiveness | Moderate effectiveness | High effectiveness | Limited effectiveness |
| Synthetic Identity Fraud | High effectiveness | Low effectiveness | Low effectiveness | Moderate effectiveness | High effectiveness |
| Bot-Driven API Abuse | Moderate effectiveness | High effectiveness | High effectiveness | Not effective | Not applicable |
| Friendly Fraud and Chargeback Abuse | Limited effectiveness | Not applicable | Not applicable | Moderate effectiveness | High effectiveness |
| Low-and-Slow Fraud Patterns | High effectiveness | Limited effectiveness | Low effectiveness | Not effective | High effectiveness |
How to Use This Matrix
This matrix demonstrates why layered fraud prevention is essential. Attacks that bypass one layer are often detected or mitigated by another later in the transaction lifecycle.
- Fraud types represent the primary abuse patterns targeting payment gateways
- Prevention layers reflect defensive controls applied before, during, and after authorization
- Effectiveness levels indicate how well each layer addresses a specific fraud type
Key Takeaway
The most resilient payment gateway risk mitigation strategies combine real-time controls, selective authentication, and post-transaction intelligence. Mapping fraud types to prevention layers allows businesses to reduce fraud losses while maintaining conversion performance and operational efficiency.
Key Metrics Used in Payment Fraud Risk Management
Without visibility into these metrics, fraud often goes undetected until disputes and penalties appear weeks later.
- Transaction velocity by card, IP, and device
- Authorization-to-decline ratios
- Retry patterns and error codes
- Chargeback frequency and reason codes
- Behavioral anomalies across sessions
Effective payment fraud risk management relies on monitoring more than approval rates. Important signals include:
The Role of AI and Machine Learning in Fraud Prevention
AI is not a silver bullet, but when combined with rules, velocity checks, and authentication layers, it significantly improves payment gateway transaction security outcomes.
- Adaptive risk scoring based on historical behavior
- Detection of new fraud patterns without manual rule creation
- Reduction of false positives that block legitimate customers
Machine learning in payments enables:
Static rules alone are no longer sufficient. Modern AI fraud detection systems analyze patterns across large datasets to identify subtle correlations humans cannot spot.
Payment Gateway Fraud Prevention Tools Compared
Different tools address different parts of the fraud lifecycle:
| Tool Type | What It Protects Against | Limitations |
|---|---|---|
| Rule-based filters | Basic misuse, known patterns | Easy to bypass, high false positives |
| AI fraud detection | Behavioral and emerging threats | Requires tuning and data volume |
| 3D Secure authentication | Liability shift, identity verification | Adds friction if misused |
| Bot mitigation | Automated attacks, scraping | Must adapt continuously |
| Chargeback prevention tools | Post-transaction disputes | Reactive, not preventive |
The most effective strategies combine multiple layers rather than relying on a single solution.
Operational Trade-Offs in Fraud Prevention Strategies
Every fraud prevention layer introduces trade-offs that are often underestimated during implementation. Overly aggressive rules reduce fraud but silently damage conversion. Excessive authentication increases security but creates abandonment and customer frustration.
Another overlooked factor is operational visibility. Teams that rely exclusively on aggregated risk scores often miss early indicators such as shifting retry behavior, sudden BIN concentration, or geographic anomalies. Effective protection depends on analysts being able to interrogate raw signals, not just final decisions.
AI-based fraud detection systems reduce manual rule management, yet they require continuous feedback loops. Without proper labeling of outcomes, machine-learning models gradually lose accuracy or reinforce existing biases. Fraud prevention is not a “set and forget” component.
Finally, fraud prevention must align with business context. What works for low-margin digital goods may be unsuitable for high-value subscriptions or marketplaces. Gateway-level controls should reflect transaction value, frequency, and customer lifetime expectations rather than apply uniform thresholds.
Compliance and Security Standards
Fraud prevention operates alongside regulatory requirements:
- PCI DSS compliance ensures secure handling of card data
- Authentication frameworks like 3D Secure authentication reduce unauthorized use
- Network monitoring requirements increase expectations for incident response
Compliance alone does not stop fraud, but non-compliance significantly increases exposure and financial penalties.
Trends Shaping Payment Gateway Fraud Prevention in 2026
Looking ahead, several trends will shape the next generation of transaction risk mitigation:
- Real-time decisioning at authorization level
- Deeper integration of AI models across networks
- Increased focus on API vulnerabilities as headless commerce grows
- Greater use of shared intelligence and consortium data
Fraud prevention is shifting from isolated merchant tools to network-wide coordination.
Case Example: Reducing Gateway Fraud at Scale
A fast-growing online merchant experienced repeated card testing attacks that overwhelmed its gateway and inflated processing costs. By implementing layered controls – velocity limits, AI-based risk scoring, and adaptive authentication – the business reduced fraudulent attempts by over 30% within three months.
The key was not a single tool, but coordinated controls aligned with transaction behavior.
Why Gateway-Level Fraud Strategy Becomes a Competitive Advantage
As malicious transaction activity becomes increasingly automated, the gap between reactive and proactive gateway protection becomes more visible. Businesses that rely solely on chargebacks and post-transaction reviews often absorb losses long after the initial impact.
By contrast, companies that embed risk prevention directly into gateway architecture can respond earlier in the transaction lifecycle. They adjust controls dynamically, reduce exposure across critical entry points, and maintain a smooth customer experience even during periods of heightened transaction risk.
Over time, this approach delivers benefits beyond loss reduction. Cleaner transaction data improves approval rates, reduces operational noise for support teams, and stabilizes relationships with processors and card networks.
In competitive markets, merchants that maintain consistent acceptance during periods of elevated transaction risk outperform those forced into emergency restrictions. A gateway-level risk management strategy therefore evolves from a purely defensive measure into an operational advantage that supports sustainable growth.
Final Thoughts
Fraud is now a mainstream case in online payments. As businesses grow, payment gateway transaction risk represents a systemic threat that can only be addressed through continuous monitoring and adaptable security controls.
Organizations that take payment gateway transaction security seriously will not only immediately reduce losses, but also preserve customer confidence and long-term growth.
Frequently Asked Questions
What is payment gateway risk exposure?
It describes how transaction gateways can be affected by unauthorized card-not-present activity, automated bot traffic, and misuse of transaction flows.
How effective is AI in preventing transaction abuse?
When used alongside other controls, AI greatly enhances the identification of sophisticated and constantly changing threat patterns.
Can payment gateways block abuse on their own?
No. Gateways deliver the technical framework, but merchants and processors are responsible for configuring controls and continuously overseeing risk management.
What is the most common gateway abuse pattern today?
High-volume automated card testing and bot-driven transaction attempts remain the most widespread forms of misuse.
Does 3D Secure remove all unauthorized activity?
It significantly lowers the risk of illegitimate transactions and enables liability shifts, but it does not address every abuse scenario.
How can businesses minimize chargebacks?
By improving transaction oversight, maintaining clear customer communication, and applying preventive risk controls throughout the payment flow.