Online card payments balance two competing priorities: frictionless checkout and strong transaction security. 3D Secure authentication was created to resolve this tension by adding an additional verification layer for card-not-present transactions, without turning every purchase into a multi-step obstacle course.
Today, 3DS payment flows are a core component of global card networks, regulatory compliance frameworks, and merchant risk strategies. Understanding how the 3D Secure system works – and how it has evolved – is essential for any business that processes online card transactions at scale.
3D Secure (3DS) is a card authentication protocol designed to verify that the person initiating an online transaction is the legitimate cardholder. It introduces an extra validation step during checkout, known as 3DS verification, before the transaction is authorized.
The name “three-domain” refers to the three-domain structure involved in every 3D transaction:
Together, these domains enable a secure exchange of authentication data without exposing sensitive card information.
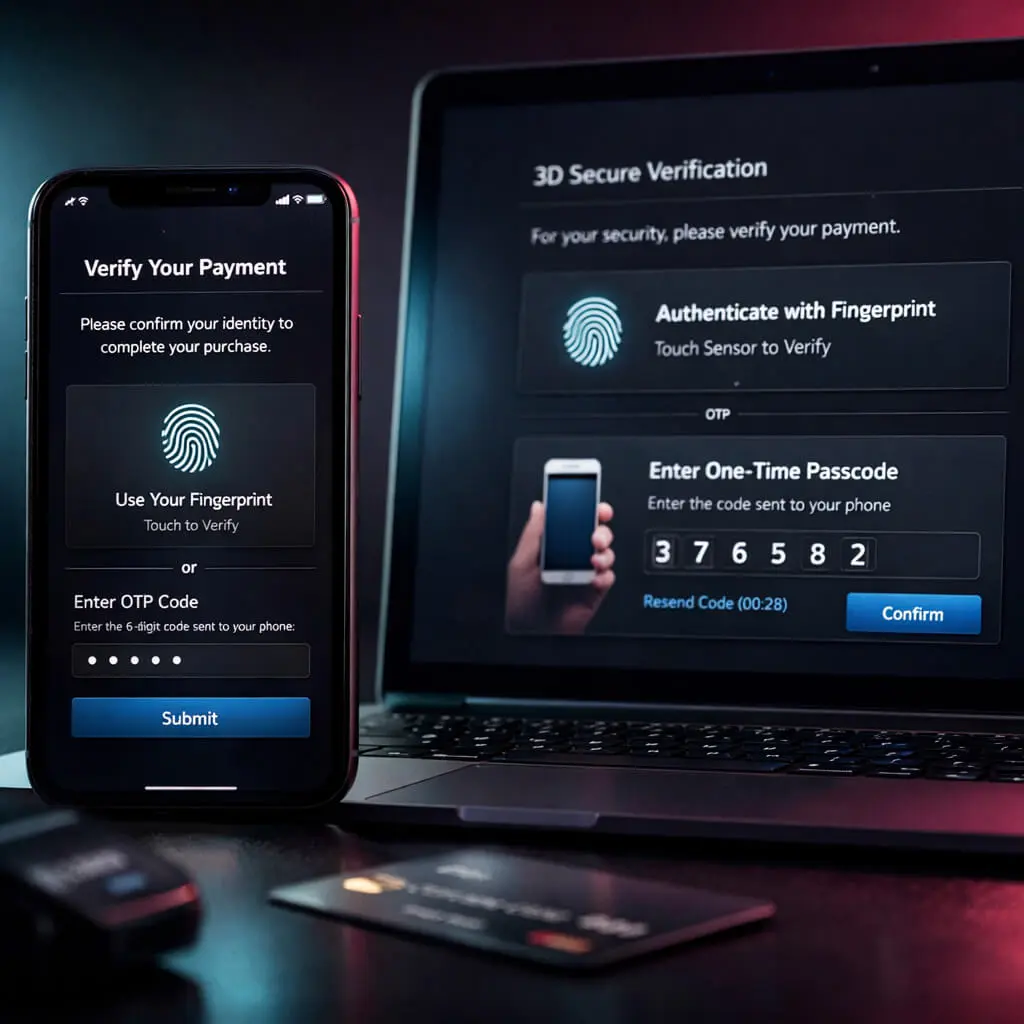
A typical 3D secure payment follows this sequence:
Modern 3DS processing aims to minimize friction by applying authentication only when risk thresholds are exceeded.
3D Secure 2.0 dramatically improved approval rates and customer experience by allowing most low-risk transactions to pass without visible challenges.
In regions governed by European regulation, Strong Customer Authentication (SCA) requires at least two independent verification factors. 3DS authentication is the primary mechanism used to meet PSD2 compliance for card payments.
SCA verification can involve:
Not every transaction requires SCA, but merchants must support compliant flows when exemptions do not apply.
Whereas PSD2 defined Strong Customer Authentication as a regulatory minimum standard, the levels set by PSD3 are likely to offer guidance on how the framework will be calibrated – not upgraded – for this era. The latest proposals include clearer rules on exemptions, greater harmonisation across member states and more closely aligning with modern authentication technologies.
This, for merchants, means 3DS is still going to be the main option for satisfying card-based authentication. The emphasis will turn toward more intelligent usage, instead of broader enforcement.
Merchants that utilize adaptive 3DS flows should experience little to no impact, where a static or legacy implementation may need alterations.
By shifting authentication responsibility to the issuer, 3DS enables liability shift, protecting merchants from certain dispute types and supporting chargeback reduction strategies.
As a fraud prevention protocol, 3DS adds issuer-side intelligence that merchants cannot access independently.
3DS is the standard mechanism for meeting SCA obligations under European regulations.
Verified transactions carry stronger trust signals, improving long-term risk profiles with processors and networks.
One of the most common misconceptions about 3D Secure is the assumption that it eliminates all transaction-related risk. In practice, 3DS addresses only a specific subset of issues tied to cardholder authentication.
It does not prevent disputes caused by customer dissatisfaction, billing errors, or unclear refund policies. It also has limited impact on so-called “friendly disputes,” where the cardholder later denies a legitimate purchase. In these cases, authentication alone does not resolve the underlying problem.
Understanding these limitations is critical. Merchants that rely exclusively on 3DS without addressing operational processes such as customer communication, refund clarity, and order transparency often see dispute volumes remain unchanged despite successful authentication rates.
In 2026, 3D Secure is no longer a “nice-to-have” – it’s simply part of doing card payments online. The real difference between PSPs is not whether they support 3DS, but how well it works in practice: fewer unnecessary challenges, smoother checkout, and enough control and reporting to actually improve conversion.
Here are PSPs that already handle EMV 3DS2 in a mature way and remain relevant in 2026:
Strong 3DS2 coverage for both web and in-app payments, clean APIs, and sensible defaults. A good fit if you want to move fast and keep things simple.
More enterprise-oriented in terms of flexibility and control: routing options, solid app support, and features that work well for regulated markets and multi-country setups.
Focuses heavily on authentication performance — helping reduce unnecessary challenges while keeping liability shift where possible, with reporting that makes optimization easier.
Built for scale, with broad issuer and network coverage, stable performance, and integration options that work even when the payment stack is complex or partly legacy.
Don’t stop at “yes, we support 3DS.” In 2026, the real questions are:
A solid 3DS implementation in 2026 should reduce fraud without hurting conversion – not force you to choose between the two.
From a merchant perspective, 3DS adoption is rarely a purely technical decision. It directly impacts checkout performance, customer perception, and revenue predictability.
Key advantages include stronger issuer-backed authentication, reduced exposure to unauthorized transaction disputes, and improved standing with acquiring banks. For merchants operating in cross-border or high-risk environments, these benefits often outweigh short-term friction concerns.
However, the drawbacks are equally real. Excessive challenge rates can negatively affect conversion, especially on mobile devices or in regions where issuers rely on outdated verification flows. Poorly tuned implementations may result in customers abandoning legitimate purchases due to confusion or authentication fatigue.
The most successful merchants treat 3DS not as a blanket security requirement, but as a conditional control – applied dynamically based on transaction risk, customer history, and contextual signals.
Despite its advantages, payment 3DS is not without drawbacks:
Successful deployment depends on using 3DS selectively, not universally.
Applying 3DS universally across all transactions may appear safe, but in many cases it produces the opposite effect. Low-value purchases, returning customers, and repeat initial card-on-file setup often carry minimal risk, yet excessive authentication in these scenarios can increase abandonment.
Merchants with mature data sets typically benefit from selective application. By limiting authentication to unfamiliar devices, unusually high amounts, or cross-border transactions, they preserve conversion while still addressing meaningful exposure.
The goal is not maximum authentication, but optimal authentication – applied only where it changes outcomes.
Modern merchants rarely implement 3DS from scratch. Instead, it is enabled through payment providers that support EMV 3DS.
Key implementation considerations:
A well-configured 3d secure site ensures authentication appears only when it meaningfully reduces risk.
In modern payment environments, 3DS is rarely implemented as a standalone feature. Instead, it is embedded into broader authorization and risk orchestration workflows.
A typical implementation includes:
One common mistake is enabling authentication for all transactions by default. This approach often leads to unnecessary friction without proportional risk reduction. Best practice is to combine 3DS with internal scoring, behavioral analytics, and exemption logic.
Equally important is post-launch optimization. Merchants that regularly review authentication outcomes are better positioned to balance security and conversion over time.
Beyond security and compliance, 3DS introduces several operational side effects that are often overlooked during implementation. Authentication flows are controlled by issuing banks, which means merchants have little influence over user interface, messaging, or verification speed.
As a result, customer support teams frequently receive inquiries related to failed or confusing authentication attempts. These interactions increase support load, especially in regions where issuer flows vary significantly or rely on outdated verification methods.
From an operational perspective, successful 3DS deployment requires coordination between risk teams, customer support, and product managers. Without this alignment, authentication can solve one problem while quietly creating others.
3DS does not prevent all disputes, but it is highly effective against unauthorized transaction claims. When authentication succeeds, liability for certain chargebacks shifts from the merchant to the issuer.
This makes 3d transaction authentication a strategic tool for high-risk verticals and cross-border commerce.
A unique characteristic of 3DS is that the merchant does not own the authentication experience. Once a transaction enters the verification stage, control shifts entirely to the issuing bank.
This structure has important implications. While merchants configure when authentication is triggered, they cannot dictate how it is presented or which verification method is used. As issuers modernize at different speeds, user experience can vary widely between transactions.
For merchants, this reinforces the importance of minimizing unnecessary challenges. The less often customers encounter issuer-controlled flows, the more consistent and predictable the checkout experience becomes.
Authentication increasingly happens in the background, using behavioral and device signals.
Issuers favor face and fingerprint verification over static credentials.
Advanced risk scoring improves exemption accuracy, reducing unnecessary challenges.
Upcoming regulation is expected to refine SCA requirements rather than replace 3DS entirely, reinforcing its role in the ecosystem.
Adoption of 3DS continues to expand beyond regulatory mandates. Industry reports indicate that a growing share of global card transactions now support EMV 3DS flows, driven by issuer readiness and increased focus on liability management.
Looking into 2026, several adoption patterns are becoming clearer. Issuers are prioritizing biometric-based verification, merchants are demanding more granular exemption control, and networks are investing in data-rich authentication to reduce false challenges.
At the same time, customer tolerance for friction remains low. This tension is accelerating investment in invisible authentication techniques, where risk is evaluated silently without interrupting checkout.
In these scenarios, 3d payment method authentication provides a balance between protection and usability.
3DS authentication has evolved from a disruptive security add-on into a foundational component of modern card payments. When implemented correctly, it strengthens transaction security, supports regulatory compliance, and protects merchants from unnecessary losses – without sacrificing customer experience.
For businesses processing online card transactions, mastering 3ds processing is no longer optional. It is a prerequisite for sustainable growth in an increasingly regulated and risk-aware payment landscape.